Workflows Overview
You can create workflows to prevent access or prompt for additional security checks such as MFA. Each workflow can contain one or more rules to determine whether the data associated with an account is valid or risky. Rules contain signals defined to check for account and event fraud information.
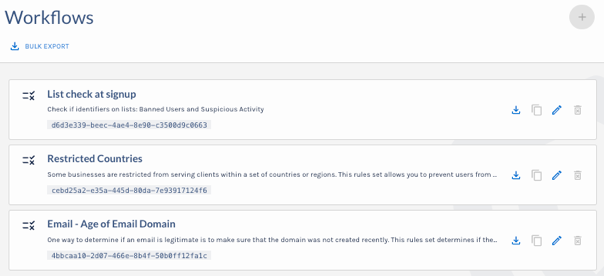
Workflows Page
For example, you may want customers to sign up for your company’s new service. Registration may require a username, email address, and phone number. To be safe, you want to ensure each email address is valid, not found in any known breaches, and not from countries your company has restricted. You could create two types of rules to perform these safety checks.
Valid Email - Create a workflow and add the following signals to check the validity of each incoming email address:
email.malicious
Is this email a known malicious account?
email.disposable
Is this email disposable?
email.breachInfo.count
Is this email present in any current breaches?
If any of these are true for an incoming email, you can set the outcome of the rule to deny access, or you could have the outcome trigger additional security checks in your registration flow.
Country Access - Create a workflow and add the following rules to determine if the IP address is associated with an account coming from a country with which your company does not do business:
ip.location.country == 'RU'
Is the IP address coming from Russia?
ip.location.country == 'CN'
Is the IP address coming from China?
If an account is coming from a restricted country, you can set the outcome to deny access and prompt for a customer-friendly message about service area restrictions.
Workflows can be created, imported, and exported in the Verosint interface or through the Rules API. Workflows defined in the Verosint interface can be exported and evaluated with the verosint tool. Imported and exported rules are in JSON format.
Using Lists with Workflows
You can create Workflows that are applied to a specific set of accounts by creating a list and adding the list to a Workflow.
Updated 5 months ago