Create a Rule Set
Drive real-time, risk-based authentication, so you can programmatically block suspicious activity without slowing down trusted users.
Create a Rule Set
Create from Templates (Imprivata Customers)
Default templates are automatically available for:
- Advanced Passwordless Access (APA) - Strict, Moderate, and Permissive versions
- Identity Assurance and Threat Detection (IATD)
These templates are also accessible in the Template Library. You can use these as a starting point or customize as needed.
Create from scratch
To create a rule set:
- Select Rule sets from the navigation pane and click the + in the top right corner of the page to either +Create or +Import a rule set.
- Enter a unique Name, an optional description, and select or input a Default Outcome. The Default Outcome defines what happens when no rules in the rule set are triggered, ensuring there’s always a clear outcome applied.
- Click Add Rule.
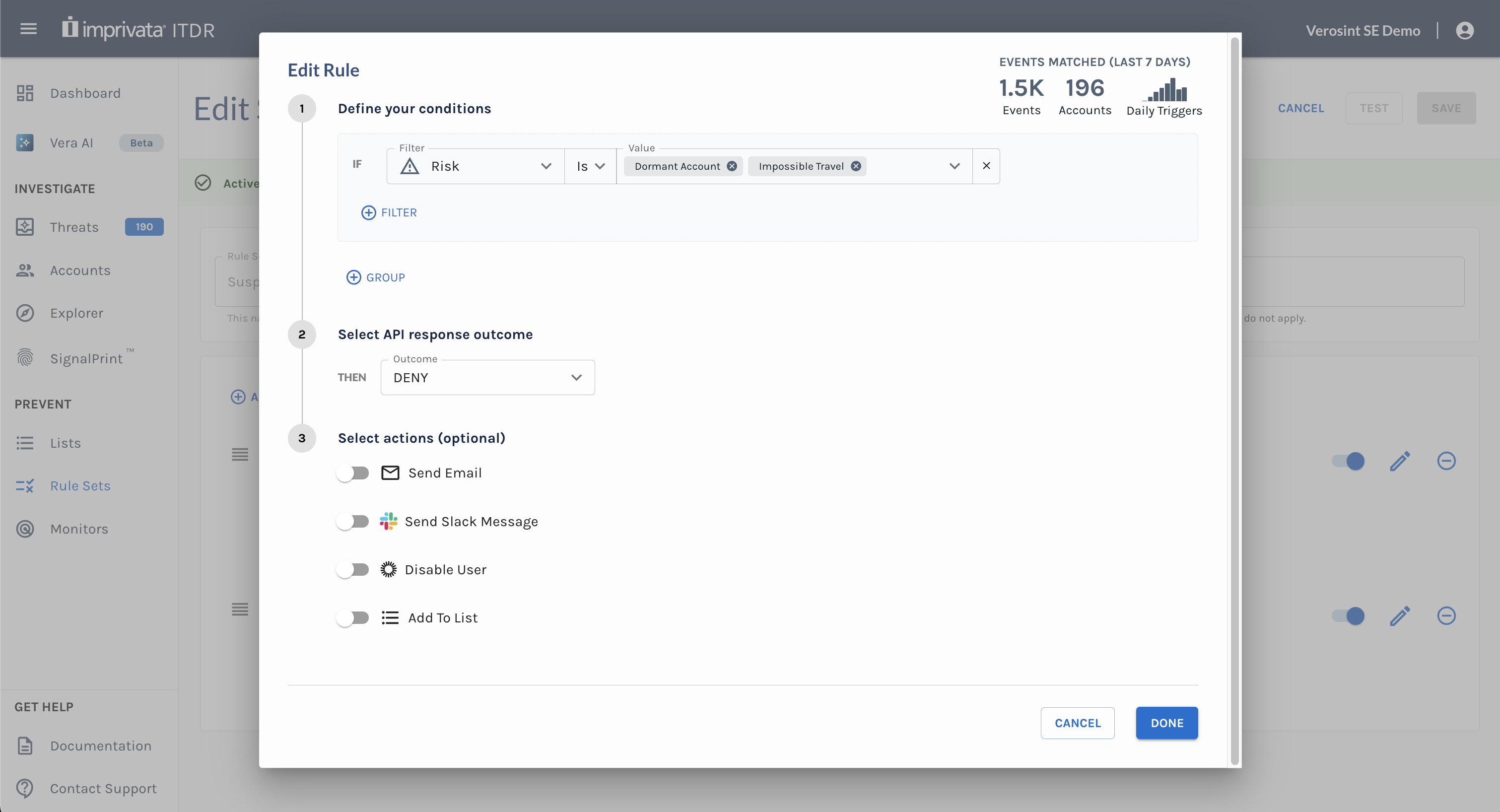
- Define your conditions using Filters. Filters (signals) are grouped by Email, IP, Phone, and User Agent categories. If you have created lists to group accounts, they are also available to add to a rule.
- Impact (Last 7 Days) displays affected events and accounts, updating instantly as you tweak your filters. This feature is not available for custom filters (CEL mode).
- Select the API response outcome. This is the string that the Verosint API will respond with if the condition is met.
- Select actions (optional). Specify actions that should trigger when the condition is met. Supported actions include:
- Send Email: Trigger an email notification to specified recipients or distribution list.
- Send Slack Message: Trigger a message to specified Slack channels.
- Send Teams Message: Trigger a message to specified Microsoft Teams channels.
- Send to Datadog: Send event details as a JSON payload to Datadog.
- Send to Splunk: Send event details as a JSON payload to Splunk.
- Send to Webhook: Send event details as a JSON payload to a custom webhook.
- Add to List: Automatically add an entity (account, session, device, etc.) to a selected List for future monitoring or investigation.
- Remove from List: Automatically remove an entity from a selected list when risk is reduced or after successful step-up authentication.
- Disable User: Automatically disable an account. This will prevent the user from accessing his/her account in your system.
- Define your conditions using Filters. Filters (signals) are grouped by Email, IP, Phone, and User Agent categories. If you have created lists to group accounts, they are also available to add to a rule.
- Hit Save. The rule set is ready for action!
Alternatively, hit Test to convert your changes into a test instead of immediately impacting production.
Required Integrations for Actions: Slack, Teams, Datadog, Splunk, Webhook, and Disable User actions only appear if those integrations are already configured in Settings.
Notification Payloads: For Datadog, Splunk, and Webhook, the event payload is identical to what you receive through your configured SIEM logs. See an example payload here.
Message Customization: To personalize your Email, Slack, or Teams messages, see Action Variables.
Add Rules to your Rule Set
Rule Sets and Auth0All properties from the Auth0 event object (
Actions Triggers: post-login - Event Object) are available to reference from Rule Sets underparameters.<Auth0 property name>. You can set an action toALLOWand have Auth0 prompt Login Success. You can also set an action toALLOW_WITH_MFAto prompt Auth0 to require MFA. Set an action toDENYto reject a login attempt.
View Active Results
After you save a rule set, you can review Active Results to see how the active version is performing in production.
Active Results gives you an at-a-glance view of real rule set activity, including total Evaluations and Users, Outcome Distribution, and Rule-by-Rule Impact. This makes it easier to understand which outcomes are happening most often, which rules are matching, and why.
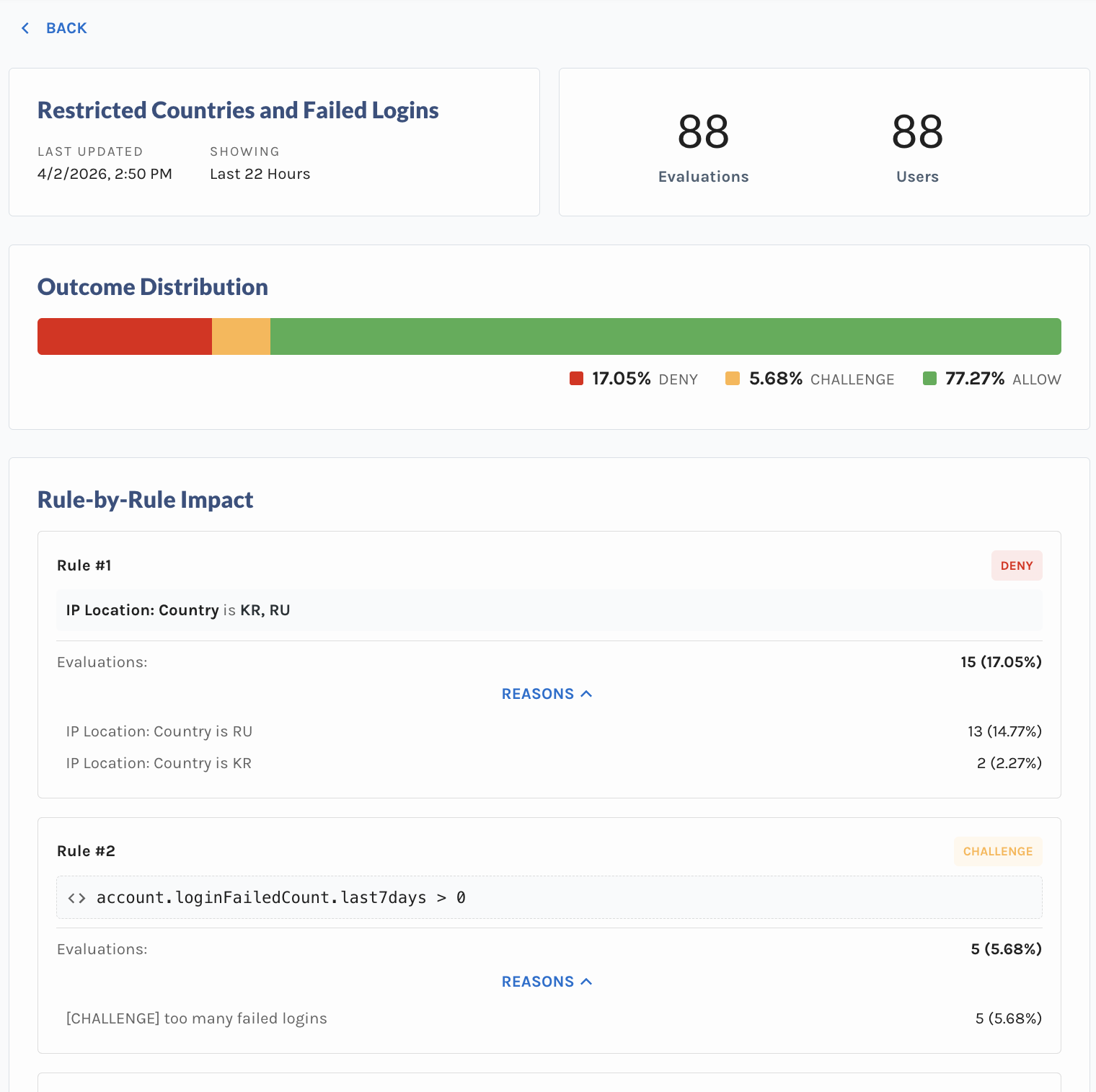
Active Results shows how the active version of a rule set is performing
Versioning
Each rule set includes a Version Number to track changes over time.
- The current version number is displayed on each rule set tile on the
/rule-setspage. - Any change to a rule set creates a new version (except the Rule Set Name and Description).
- Versions increment automatically when rules, conditions, outcomes, and/or actions are modified.
Rule Sets and Auth0All properties from the Auth0 event object (
Actions Triggers: post-login - Event Object) are available to reference from Rule Sets underparameters.<Auth0 property name>. You can set an action toALLOWand have Auth0 prompt Login Success. You can also set an action toALLOW_WITH_MFAto prompt Auth0 to require MFA. Set an action toDENYto reject a login attempt.
Updated 24 days ago